DIY vs Buy: A Short Guide on Toolchain Validation for Functional Safety
When most people think about functional safety, the first image that comes to mind is hardware redundancy: That stuff is…
Jacob's Blog
Category Archives: Security

When most people think about functional safety, the first image that comes to mind is hardware redundancy: That stuff is…

Many embedded systems today must be secure. Many of these devices also have complex timing requirements that also require an…

As 2022 creeps to a close, many of you probably reflect on what went right and what didn’t. You’re probably…

In “5 Elements to a Secure Embedded System – Part 4 Secure Bootloaders,” we continued to discuss the five elements…
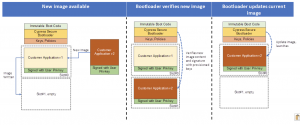
In “5 Elements to a Secure Embedded System – Part 3 Secure Boot”, we continued our discussion about the five…
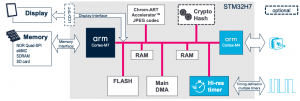
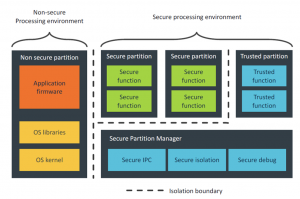
Multicore microcontrollers are starting to become popular among embedded systems designers. Designers can leverage multiple cores by breaking their applications…
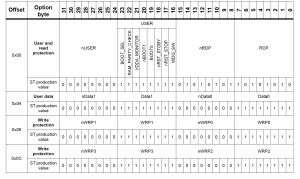
Nearly every microcontroller contains option bytes, fuses, or some method to control general settings on the processor. These settings often…
Developing a product today without taking security into account is foolhardy. Nearly every device being developed today is in some…
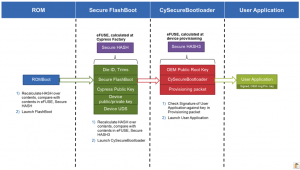
In “5 Elements to a Secure Embedded System – Part 2 Root-of-Trust”, we continued our discussion about the five essential…

In “5 Elements to Secure Embedded Systems – Part #1 Hardware-Based Isolation”, we started our discussion about the five essential…
Nearly every embedded system requires some level of security, whether it’s just the basics to lock down the programming port…

The Webinar Recording can be accessed at the following link: Click here to Watch Webinar On-Demand Webinar Description One of…