5 Elements to Secure Embedded Systems – Part #3 Secure Boot
In “5 Elements to a Secure Embedded System – Part 2 Root-of-Trust”, we continued our discussion about the five essential…
Jacob's Blog

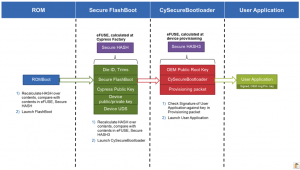
In “5 Elements to a Secure Embedded System – Part 2 Root-of-Trust”, we continued our discussion about the five essential…

Last month, in 3 Tips for Speeding Up Framework Interrupt Handlers, we looked at several methods that could be used…

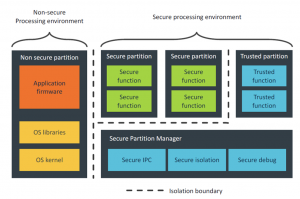
In “5 Elements to Secure Embedded Systems – Part #1 Hardware-Based Isolation”, we started our discussion about the five essential…

Development teams today are faced with the need to develop systems within smaller budgets, shorter timeframes and with more features….

Embedded software developers today are a bit spoiled. Many microcontrollers come with an ecosystem that includes peripheral drivers, an RTOS,…

If a developer closely looks at framework and library files, they may come across functions that have __weak in front…
Nearly every embedded system requires some level of security, whether it’s just the basics to lock down the programming port…
My favorite line from the Matrix is that “there is no spoon”, and today that is a wise statement for…

The advancements in chip, sensor and wireless technologies over the past decade have resulted in exponential increases in system complexity…

Delivering embedded systems on-time is a struggle for many developers and teams. From time-to-time, I’ve struggled with delivering on-time as…

Machine learning is quickly finding applications in the microcontroller space. Machine learning is a completely different paradigm in application development….

Buffer overflows are one of those bugs that wreak havoc on embedded software. The system appears to be working perfectly…